WhatsApp fixed the issue soon after the vulnerability was patched
WhatsApp has corrected a flaw that may have revealed sensitive information about users, including personal conversations, through the use of a created picture. Checkpoint Research notified WhatsApp of a vulnerability in the image filter function of WhatsApp for Android and WhatsApp Business for Android.
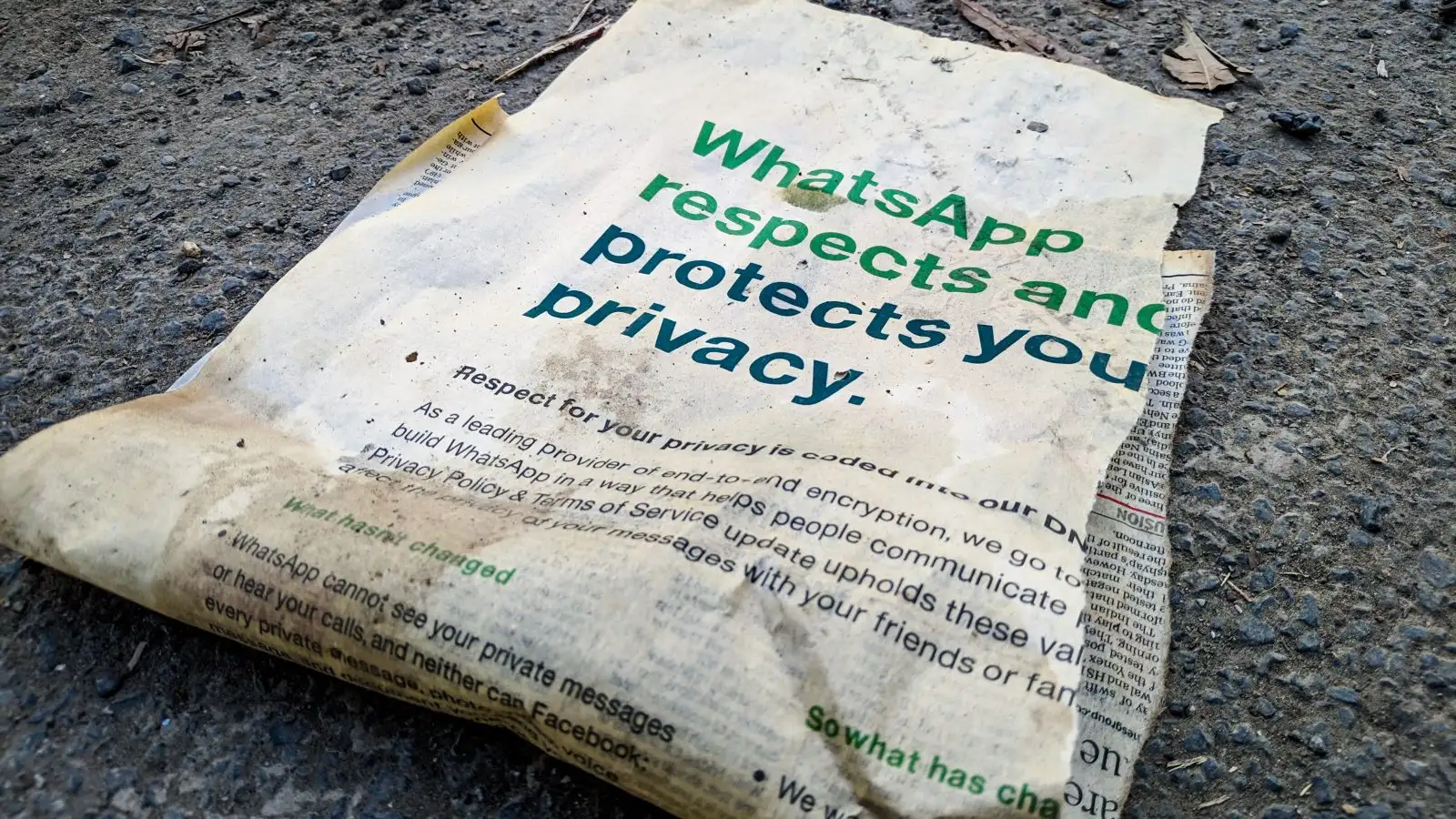
Even though the Facebook-owned messaging service patched the flaw as soon as it was discovered, the weakness might have been exploited even in an end-to-end encrypted discussion.
According to a CheckPoint Research study, if the vulnerability discovered in the picture filter feature had been exploited, hackers might have accessed sensitive information from users’ computers. On November 10, 2020, WhatsApp was notified of a vulnerability in its system. In February, a fix for the problem was released.
“Daily, about 55 billion messages are exchanged and received on WhatsApp, with 4.5 billion images and 1 billion videos being shared on the platform. We concentrated our investigation on how WhatsApp handles and delivers photos. Then we utilized our AFL fuzzing lab at Check Point to produce malformed files for a variety of image kinds such as BMP, ico, gif, jpeg, and png, before moving on to the next image type “
According to the cybersecurity firm, the hack necessitated “complex procedures and considerable user interaction” to be successful. To obtain access to the vulnerability, the attacker may have simply emailed an attachment containing a specific malicious picture to the recipient’s email address.
“After performing some reverse engineering on the crashes we received from the fuzzer, we discovered an unusual crash that we determined to be caused by memory corruption. Before we started our research, we reported the problem to WhatsApp, who provided us with a name for the vulnerability: WhatsApp Security Vulnerability. CVE-2020-1910 Out-of-bounds read and write on a heap-based system. Important to note about this situation is that it might have resulted in the release of sensitive information from the WhatsApp application if the circumstances were not so unusual and complicated,” according to the study.
The attackers, on the other hand, were able to obtain access to the vulnerability that WhatsApp had addressed. Checkpoint research was credited with revealing the problem on time, according to the Facebook-owned messaging service.
“This report summarizes several procedures that a user would have been required to complete, and we have no reason to assume that users were adversely affected by this problem. Having said that, even the most complicated circumstances that researchers come across may be used to help consumers feel more secure.
Like any technological product, we suggest that customers keep their applications and operating systems up to date, download updates as soon as they become available, report suspicious messages, and get in touch with us if they encounter any difficulties while using WhatsApp,” the company stated in a statement.