What is a DDoS attack? How does DDoS work?
Today, every piece of information we share on the internet is being saved somewhere on the server. It is very important to keep servers alive to access that information. Some information can be shared with anyone but some of them are very important for us and we can’t let anyone know. Hackers always try to get private information to do their dirty work.
But, Hacking is not just about stealing information. When hackers do not get success in stealing, they try to destroy the whole server. In this case, we may lose all the information on the server if we don’t have any backup or a proper defense.
Table of contents
What Is a DDoS attack?
Nowadays, we hear a lot about attacks on gaming networks, news websites, bank websites, etc. And when I write about those attacks I mention one term that is ‘DDoS’. Many readers may have already known about ‘DDoS’ attacks but many of them are still not aware and they always ask me: What is DDoS?
So in this article, I am going to explain everything you need to know about DDoS attacks. If you will have any questions, you can ask in the comment section.
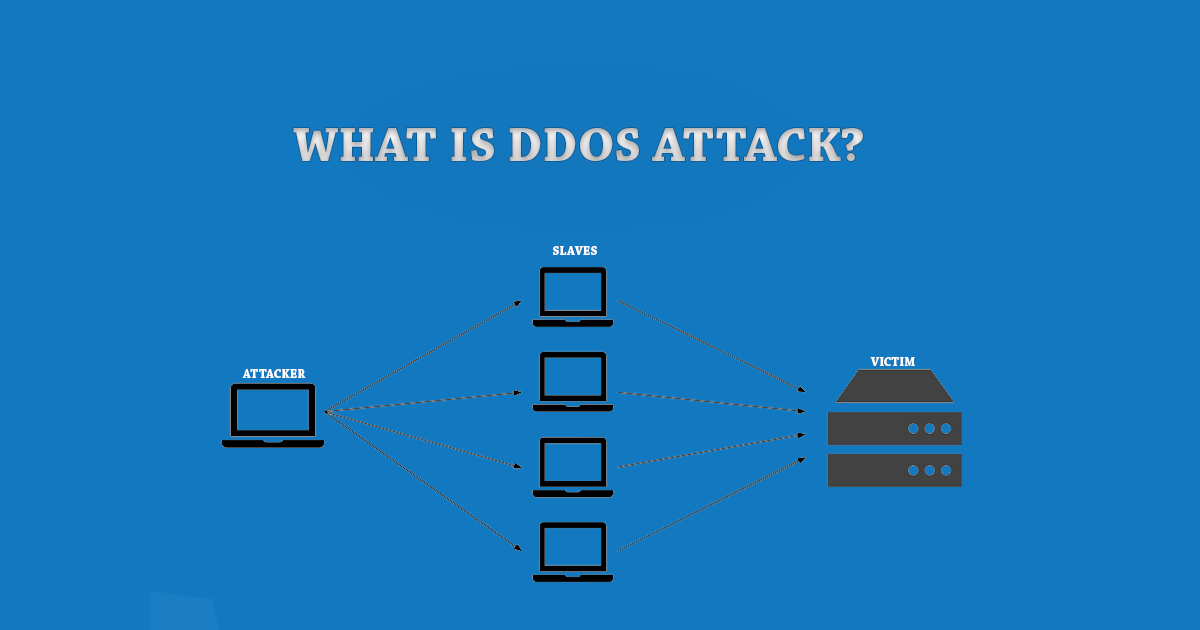
Distributed denial of service (DDoS) attack refers to the attempt to make online service unavailable through overwhelming it with traffic from numerous sources. DDoS attack targets a wide range of important resources including news websites, banks, and many more. They pose a challenge to people’s attempts to access or publish important information.
A decade ago, DDOS was only a basic attack that trying to overwhelm connection with traffic with the aim of taking a certain web property offline. When leading web experts began fighting DDoS attacks in the year 2000, the flood attacks ranged at 400 Mbps but as we speak they exceed 100 Gbps.
The attackers build a network of infected computers called botnet and spread the malicious software through websites, emails, and social media. The machines are capable of being controlled remotely once infected without the knowledge of the owners. These machines are then used as the army in launching an attack against the target. Some botnets are as strong as millions of machines.
The floods are generated in numerous ways including sending more connection requests that exceed what a server can handle. They can also be generated by having the computers send to the victim a huge volume of random data with the intention of using up the target’s bandwidth. Some DDOS attacks are so huge that they can max out the whole country’s international cable capacity.
Specialized online marketers exist who buy and sell individual DDoS attacks or botnet. By using these marketplaces, anyone can pay some fee in order to silence websites that they disagree with or to bring to complete halt online operations of a particular organization. A week-long DDoS attack for instance that is capable of bringing a small firm offline could cost as little as $200.
Beyond the democratization of DDoS attacks are the advanced techniques and targets. Today DDoS involves a series of attacks targeting multiple devices that consist of the organization’s security infrastructure as opposed to targeting connection bandwidth only. They include various applications and firewall or IPS devices that organizations rely on such as DNS, SMTP, VOIP, HTTPS, and HTTP.
The latest version of the DDOS attack is the common multi-vector attack that combines flood, state exhaustion, and application attacks against the infrastructure devices in a sustained single attack. These attacks have gained popularity due to their effectiveness and the fact that they are hard to defend against.
Today’s new realities of DDOS attacks require new approaches to defense. Network experts have been at the forefront in looking for ways to combat DDOS attacks for some years now. The best defensive mechanism against the modern DDOS attack is the layered approach combining cloud-based protection and on-premise. With this type of protection, you are guaranteed 100% security for your organization against the entire spectrum of DDOS attacks.
A digital attack map is also ideal for protection against a DDOS attack because it displays global DDOS activities on any particular day. It displays the attacks as dotted lines that are scaled to size and stored in line with their source and the destination countries of attack traffic when they are known.