How to Become an Ethical Hacker in 2025?
In the past few years, the risks of cyber attacks and hacking attempts on websites and networks have risen by many folds. Today, there is not a week that passes by without reports of any website or network being hacked. The hacking attacks are getting advanced with each passing day, which has created a headache for businesses and organizations since they cause great losses.
In fact, a study states that more than 60% of small businesses go bankrupt and close down within 6 months after a cyber attack. This is a testament to the fact that cyber-attacks are in fact very dangerous for organizations and businesses. So, is there no way to stop these attacks from damaging organizations and stealing sensitive data?
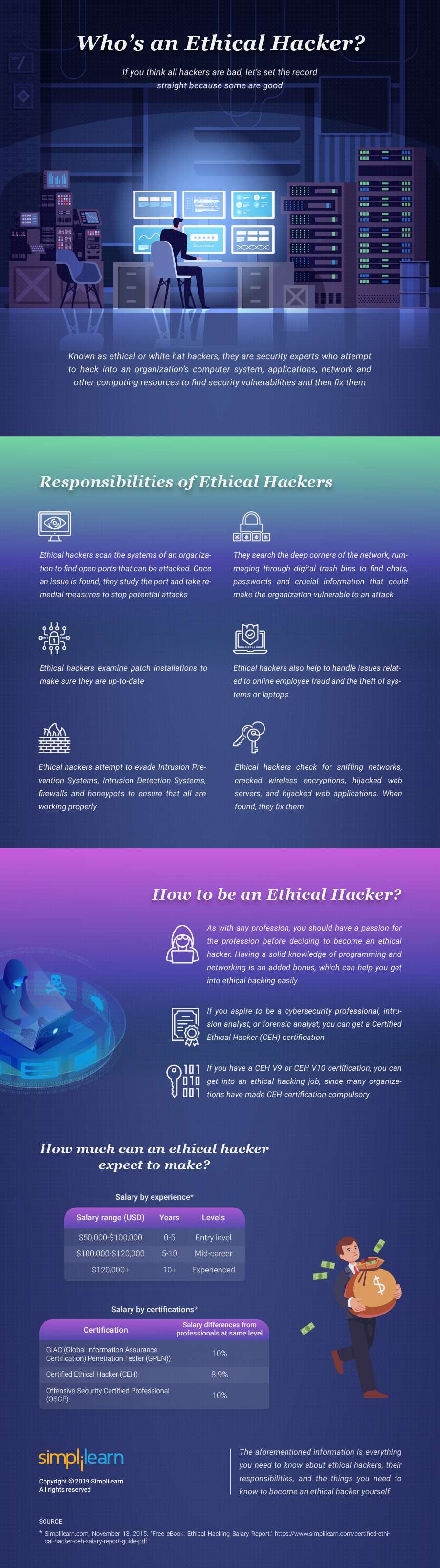
Certainly not, there are many ways in which these cyberattacks can be stopped. Out of those, the best way of stopping cyber attacks is by hiring a hacker or being one. Yes! You read it right, hiring an ethical hacker or being an ethical hacker yourself can save your organization or website from the ever-increasing risks of cyberattacks. Confused? Well, an ethical hacker is a professional who hacks websites or networks to ensure that they are safe from attacks from rogue hackers, black hat hackers, or even crackers.
Table of contents
Ethical Hackers Vs Crackers
Now that you know not all hackers are bad, you might be interested in knowing what differentiates the categories of hackers. Well, to put things in perspective, ethical hackers or white hat hackers are programming professionals who penetrate into websites and networks to find vulnerabilities and fix them.
On the other hand, crackers or black hat hackers are those people or groups of people who have hideous intentions, like stealing sensitive information, penetrating into a network to damage it, and others. In short, ethical hackers are the good hackers who help find vulnerabilities and fix them, while crackers are the hackers who leverage these vulnerabilities in an attempt to harm organizations or website/network owners.
How to start your career as an ethical hacker?
Now that you know the difference between an ethical hacker and a cracker, it is clear that technically skilled professionals with the intention of solving problems and preventing cyber-attacks are the need of the hour. Most organizations and businesses are on the look for ethical hacking professionals who can ensure that their websites and networks are secure against cyber attacks.
This has created a plethora of opportunities for people well-versed in the ins and outs of ethical hacking or hacking in general. However, not everybody who wants to be an ethical hacker can become an ethical hacker. There are certain skills that an individual needs to acquire to become an ethical hacker. If you are interested in becoming an ethical hacker, here are a few tips that can help you get started:
Getting started
The first thing you need to do while starting your journey to becoming an ethical hacker is decide the field you want to work in. An ethical hacker can work in various industries and each industry has its specific requirements. For example, if you wish to work in the IT sector as an ethical hacker, it is better if you have an idea about how IT works.
Once you find a niche that you are interested to work in, all you need to do is start with the basics. Although it’s not necessary, learning certain courses or programming languages can help you a great deal, like CCNA, Network+, and others providing you with knowledge about networks and websites. Also, programming languages, like C, Java, LISP, and Perl, can help your cause.
Once you are well-versed in these programming languages and networking skills, you can learn the skills required for penetration testing, which is the most important skill that an ethical hacker must have.
Soft skills
If you think that ethical hacking is all about programming and technical knowledge, you need to reconsider it. Ethical hacking also requires so-called soft skills, like any other job. Being an ethical hacker requires great problem-solving skills, strong work ethics, and even better communication skills.
Also, it requires you to be street smart, which is very important when there is any situation. This is why you need to acquire these soft skills that can help you gain all the skills required to become an ethical hacker.
Stay ethical and legal
The whole point of being an ethical hacker is to be legal and never indulge in black-hat hacking techniques. You need to understand that you cannot attack any network or website without permission. Indulging in any illegal hacking attempt can lead to you being convicted which can bring an end to your ethical hacking career. So, you need to make sure that you stay legal at all times.
Get Certified
While it is not mandatory for you to get certification to become an ethical hacker, owing to the benefits of a certification, it is recommended that you get one. A certification in ethical hacking increases your chances of you getting a job. Also, it is proof for the companies hiring that you are well-versed in the nuances of ethical hacking. The certifications will help you learn and understand security and how an ethical hacker should think.
However, getting a certification is not as easy as you may think. This is where a certification training course can be of much help. Today, you can find various online certification providers, having various certification training courses, like the Ethical Hacking Course of Simplilearn. These training courses help you learn how Trojan horses, backdoors, viruses, SQL injections, and other hacking techniques work. Certification courses ensure that you are well-versed and prepared to stop all kinds of cyberattacks.
There you go, the aforementioned tips can help you become an ethical hacker and even pursue a career in ethical hacking.