19-Year-Old WinRar Flaw Left Millions of Users Vulnerable
WinRar is one of the most popular utility software used to view, create, extract archives in multiple formats like ZIP, RAR, etc. The program is quite useful and people have been using it for more than two decades. However, a recent bug in this software has questioned the security of this popular program in various ways.
As per a report by security research company Check Point, Winrar has a serious security flaw that has remained unfixed since 2005. The bug creates a loophole that can be used by black hat hackers to plant malware within your system and gain full access.
Table of contents
The bug was Found During a Fuzz Test
The vulnerability is found during a fuzz test performed by the company. If you don’t know, fuzz tests are actually a part of stress testing, where people feed random data to the software to test the limit and provoke software crashing.
The flaw provides attackers full privilege to extract .exe files into the startup folder of a computer. In this way, they ensure that the programs will automatically run at the time of booting the computer.
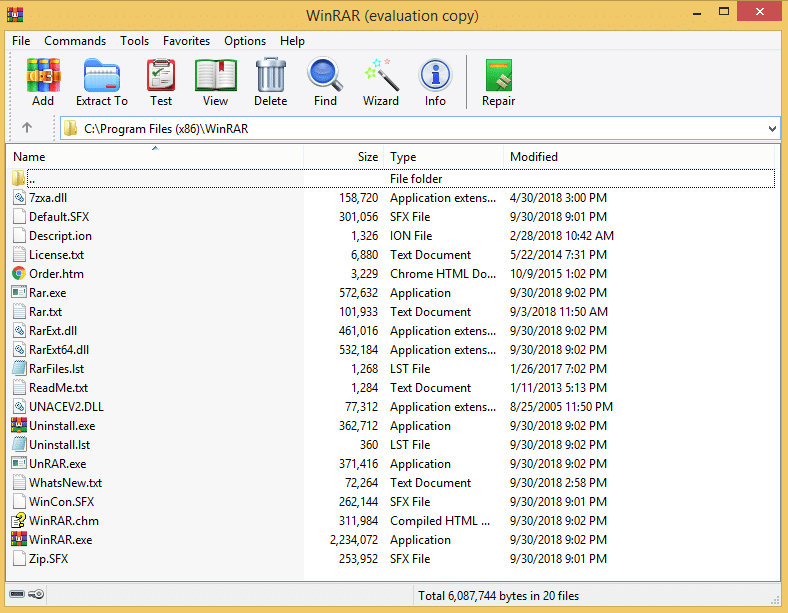
Going a little deeper, the researchers have found that the bug was actually caused by an Old DLL (Dynamic Link Library) that was used to process files compressed in ACE format.
The vulnerability has actually put millions of users around the world at risk. The bug seems even threatening after knowing the fact that malicious ACE archive can be renamed into RAR format without losing the exploit.
Also Read: 10 Types of Viruses That Can Harm Your Computer or Smartphone
How to be Safe?
After explaining the bug through a blog post, WinRar has taken immediate action and fixed the vulnerability by removing support for the ACE format. If you are a Winrar user, you must update to the latest version (5.70 beta 1) released by the company the last month.
After this step, it seems that the Winrar was using a third-party tool for ACE archives which wasn’t updated since 2005. Anyway, 19 years is a pretty long time and you should feel responsible for users who believe you and using your products.