Protecting Your JAVA Code from Vulnerabilities

Java is a widely used programming language for developing robust and scalable applications. However, like any other software, Java applications are also vulnerable to security risks if not developed and implemented properly. Cyber threats, such as hacking, data breaches, and malicious attacks, pose significant risks to Java applications and the sensitive data they handle. To safeguard your Java applications and protect them from vulnerabilities, it is essential to follow best practices for Java security.
In this article, we will explore key Java security best practices to prevent vulnerabilities in your code and ensure the security of your Java applications.
So, Let’s go !
Table of contents
1. Keep Your Java Development Environment Up-to-Date
Regularly updating your Java development environment, including the Java Development Kit (JDK) and other libraries, is crucial for staying protected against known security vulnerabilities. New updates often include important security patches that address identified vulnerabilities and provide fixes to known security issues. Therefore, it is recommended to keep your Java development environment up-to-date with the latest releases and security updates to ensure the highest level of security for your Java applications.
2. Regularly Test and Update Dependencies
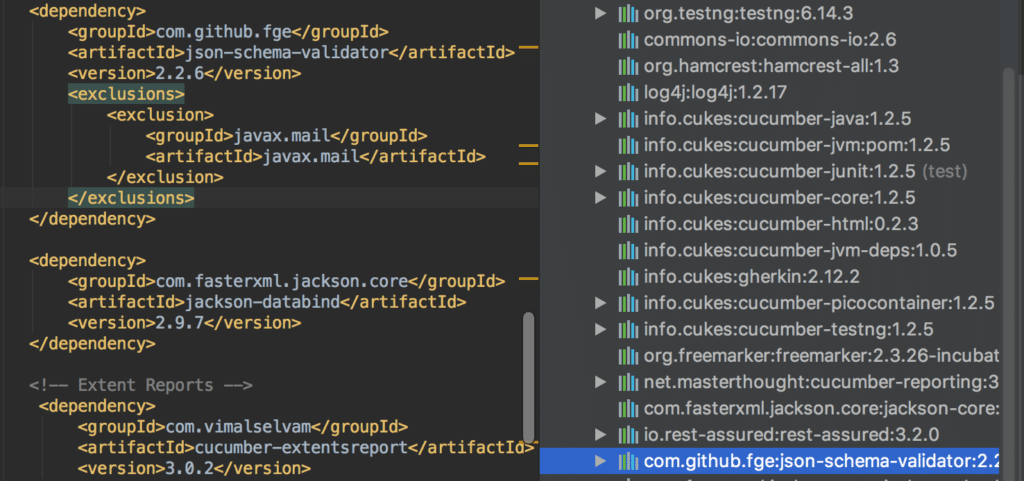
Java applications often depend on third-party libraries and frameworks, which can introduce potential security risks if not kept up-to-date. Regularly test and update all dependencies used in your Java application to the latest versions, as newer versions may include important security patches and fixes. Keep track of security advisories and vulnerability reports related to the libraries and frameworks you are using, and promptly address any identified vulnerabilities by updating to the latest secure versions.
3. Use Proper Exception Handling
Exception handling is an important aspect of writing secure Java code. Properly handle exceptions in your code to prevent information leakage and potential security vulnerabilities. Avoid displaying detailed error messages or stack traces in production environments, as they can provide valuable information to potential attackers. Instead, log exceptions securely or display generic error messages to users without revealing sensitive information about the application’s internal workings.
4. Encrypt Sensitive Data
Sensitive data, such as credentials, credit card details, and personal details, should be encrypted to protect it from unauthorized access. Use strong encryption algorithms and ensure that sensitive data is encrypted both during transmission and storage. Avoid storing sensitive information in plain text or weakly encrypted formats, and always use secure encryption libraries or APIs provided by Java for implementing encryption and decryption functionalities.
5. Implement Strong Authentication and Authorization Mechanisms
Authentication and authorization are critical aspects of securing Java applications. Implement strong authentication mechanisms to verify the identity of users and ensure that only authorized users can access sensitive functionalities or data. Use secure authentication protocols, such as OAuth or OpenID Connect, to protect user credentials and avoid the use of weak or default passwords. Employ role-based access control (RBAC) or other authorization mechanisms to restrict access to sensitive operations or data based on the user’s role and privileges.
The Takeaway
By prioritizing Java security best practices and proactively addressing potential vulnerabilities, you can safeguard your Java applications from cyber threats and protect your code and data from unauthorized access, data breaches, and malicious attacks. Stay vigilant and stay informed about the latest security updates, patches, and best practices in the Java ecosystem to ensure that your Java applications remain secure and resilient in the ever-evolving threat landscape of today’s digital world.
Remember, securing your Java applications is an ongoing process that requires constant attention and updates. By incorporating these Java security best practices into your development process, you can build robust and secure Java applications that stand up to the challenges of modern cybersecurity threats.