GitHub to release new tools for fixing flaws in projects
Open-source software provides a high level of security, for example – GitHub. Unlike executable files that can only be viewed by their own programmers or developers, open-source projects may be tested by anyone.
In reality, open source isn’t a solution. Now, GitHub is releasing new tools for its GitHub Advanced Security suite, making it easier to find flaws in open source projects hosted on its site. Open source programming poses certain security issues. In practice, not enough experts are looking at it.
And open-source projects are usually ad hoc, with no defined mechanism for reporting vulnerabilities or resources for patching them. You may not even know who is using your open source code and requires a fix.
“A lot of what we speak about is there’s a vulnerability, what’s the procedure for that issue,”
“The nirvana is not introducing the vulnerability. You stop it from happening. We should be able to help developers avoid bringing this problem, but as a software industry, we haven’t yet.”
explains Jamie Cool, GitHub’s security vice president.
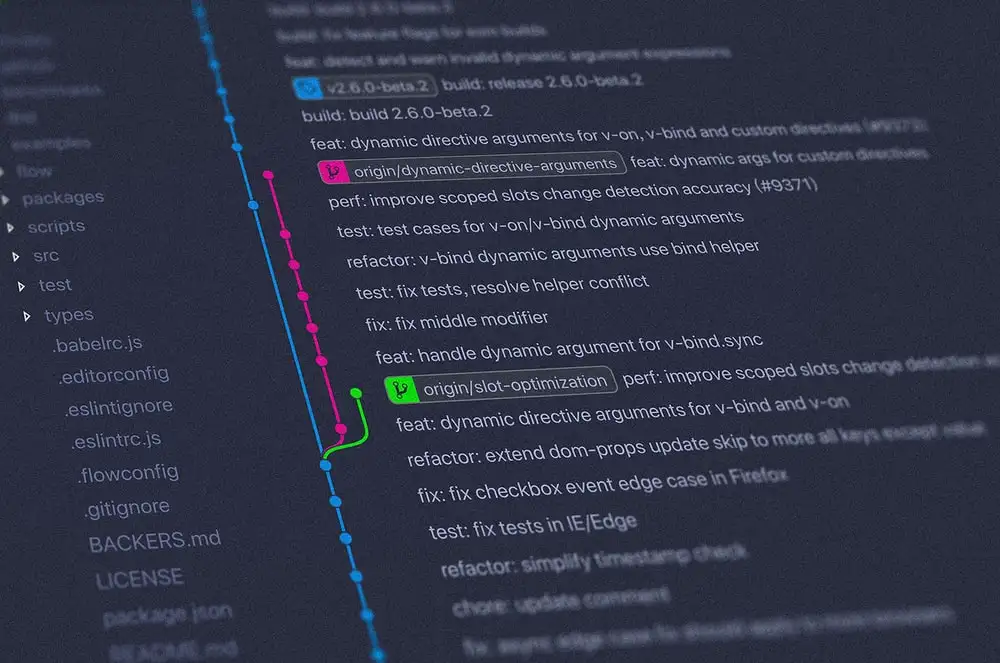
GitHub bought Semmle in September to help its community automatically detect common security vulnerabilities.
These services identify possible vulnerabilities in code, explain why they can be exploited, and describe how to repair them. Semmle’s technique may be utilized manually by security researchers as well as automatically.
GitHub’s objective is to employ Advanced Security as both a developer warning system and a bug hunting framework. GitHub Advanced Security additionally scans user “repositories” for sensitive data like passwords and private keys that shouldn’t be exposed. They work with companies like Amazon Web Services and Alibaba to identify authentication tokens automatically.
Public repositories have had this feature for some time, but today GitHub adds support for scanning private repositories.
According to GitHub, 8% of active public repositories had a secret revealed in the previous month. With these new capabilities, GitHub is tackling massive security concerns. While not all open source projects use GitHub, the site is widely used as a community social network as well as a development tool.
By providing Advanced Security, GitHub may enable more open source projects to benefit from the same tools that major corporations use to improve and secure their proprietary code.
“Most maintainers are accidental,” says GitHub CEO Nat Friedman.
“They create something, it becomes widely utilized, and suddenly they are in charge of computer security for banks or governments. They may not have a security background, but we must ensure the code they publish is secure. So the problem is to automate and naturalize it.”
Despite the importance of identifying more security problems across GitHub projects, today’s software is still linked. Not every software product is written from scratch, but rather a combination of proprietary and open-source code.
Your fitness tracker, smartphone, and automobile all have open source components from various developer projects in addition to proprietary hardware and software. Due to these interdependencies, reporting vulnerabilities and delivering fixes to the proper locations remains a challenge.
GitHub established Security Lab in November to assist the community monitor issues and automate the patching process. While GitHub can have a big effect on how the open-source community handles security, Chris Wysopal, CTO of software auditing firm Veracode, says the company’s success doesn’t excuse the rest of the industry.
“The thing with GitHub is that it’s naturally open,” Wysopal explains. “Nothing prevents a third party from checking all GitHub repositories for vulnerabilities and informing project maintainers.”
That would be costly. GitHub claims providing free vulnerability screening and analysis tools in Advanced Security costs millions. But the business believes its own investment can demonstrate the value of open source security.
